How To Install ProFTPD on CentOS
We explain all the steps to know how to install, create users and groups and enable TLS ProFTPD on CentOS.
One of the utilities that we have available to add even more security in the FTP connection is ProFTPD which we will analyze today in CentOS.
What is ProFTPD?
ProFTPD is an FTP server software under a highly configurable GPL license to meet connection expectations anywhere.
ProFTPD is designed from scratch so it does not use another copy and this gives us the possibility to configure many options in its execution.
Step1: Install EPEL on CentOS
The first step to take is to install the EPEL repository for later from obtaining ProFTPD, for this we execute the following:
yum -y install epel-release
Now, let's import the GPG key of EPEL using the following line:
rpm --import /etc/pki/rpm-gpg/RPM-GPG-KEY-EPEL-7
We proceed to update the system packages:
yum -y update
Step 2: Install ProFTPD
The next step will be to install the utility ProFTPD and OpenSSL by executing the following:
yum install -y proftpd openssl proftpd-utils
Once this process is concluded, we will run the following lines:
systemctl start proftpd.service systemctl enable proftpd.service
Step 3: Configure Firewall
If Firewalld is installed in CentOS, we must configure it with firewall-cmd to open the FTP port in the following way:
firewall-cmd --add-service=ftp --permanent firewall-cmd –reload
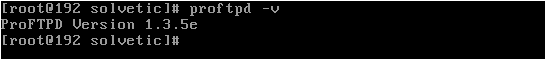
We proceed to verify the installed version of ProFTPD:
proftpd -v
Step 4: Create Users & Group for ProFTPD
Once installed ProFTPD in CentOS, is to create the group and user for access, in this case we will create a group ftpgroup and a user user1 for ProFTPD, and we will define / ftpshare as home directory for the user generated:
groupadd ftpgroup useradd -G ftpgroup user1 -s /sbin/nologin -d /ftpshare passwd user1
There we must enter and confirm the respective password for the new user. Once this is done, we will grant the permissions to ftpshare by executing:
chmod -R 1750 /ftpshare/
Step 5: Enable TLS in ProFTPD
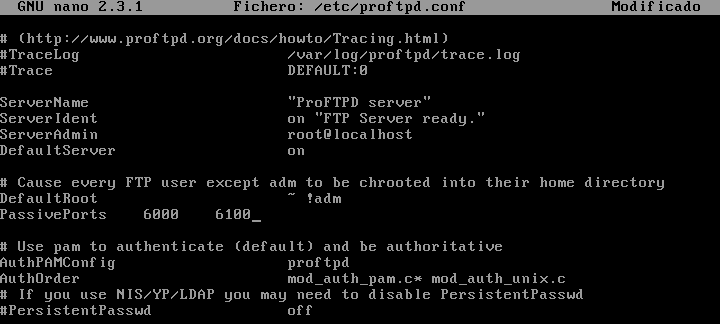
Now we need to secure the FTP connections using TLS and to do so, we must open the file /etc/proftpd/proftpd.conf but it is ideal before editing the file, creating a backup copy of the original file and then editing the file with nano .
To create the copy we execute:
cp -pf /etc/proftpd.conf /etc/proftpd.conf.bak
To access the file we will use nano and execute:
nano /etc/proftpd.conf
In the displayed file we will enter the following under the DefaultRoot ~! Adm line:
PassivePorts 6000 6100
In addition to this, we will comment on the following lines:
#<IfDefine TLS> TLSEngine on TLSRequired on TLSRSACertificateFile /etc/pki/tls/certs/proftpd.pem TLSRSACertificateKeyFile /etc/pki/tls/certs/proftpd.pem TLSCipherSuite ALL:!ADH:!DES TLSOptions NoCertRequest TLSVerifyClient off TLSRenegotiate ctrl 3600 data 512000 required off timeout 300 TLSLog /var/log/proftpd/tls.log # <IfModule mod_tls_shmcache.c> # TLSSessionCache shm:/file=/var/run/proftpd/sesscache # </IfModule> #</IfDefine>
We save the changes using the Ctrl + O keys and exit the editor using the Ctrl + X keys.
As we can see, ports 6000 and 6100 have been added to allow the passive mode of ftp, to allow this access we will execute the following:
firewall-cmd --add-port=6000-6100/tcp --permanent firewall-cmd --reload
If we want to see the state of the ports we can run the following:
firewall-cmd --list-ports
Now, it will be necessary to configure SELINUX in order to allow the reading and writing of the files, we execute the following:
setsebool -P allow_ftpd_full_access=1
To use TLS, it will be essential to create an SSL certificate, this will be built in the path / etc / pki / tls / certs, as follows:
openssl req -x509 -nodes -newkey rsa:1024 -keyout /etc/pki/tls/certs/proftpd.pem -out /etc/pki/tls/certs/proftpd.pem
The following questions will be displayed where we will enter answers such as:
- City
- Country
- Organization
- Mail and more
Now, for security reasons, we will configure the certificates so they are only legible like this:
chmod 0440 /etc/pki/tls/certs/proftpd.pem
Finally, we restart the ProFTPD service by executing the following:
systemctl restart proftpd.service